Crypto 839: Personal Notes C1
"A security system is only as strong as its weakest link"
Attack Tree: Organizing a tree in a way to see/monitor weakest points.
- Insight to possible lines of attack
- Always part of a larger tree
Weakest link property: Strengthening anything but weakest link can be useless
Defense-in-Depth: Worth strengthening multiple links (if 1 fails others exist)
Threat modeling: No such thing as perfect sec: Just a sufficient level of
Cryptography/Cryptology:
- From root word kryptos meaning hidden
- From root word grafo meaning write
The study of message secrecy and the process or skill of communicating or deciphering secret writings or ciphers. Cryptography is a way of encoding a msg so it isn't readable to anyone but the recipient
History:
Cryptography is at least 3,000 years old and there has been a primary need for it, but until the 20th century it was mostly reserved for mil/gov.
Mono-Alphabet Substitutions:
Primitive cryptographic algs. that substitute 1 char of cipher text for each char of plain text. Examples: Caesar, Atbash, Affine, ROT13
Caesar Cipher:
First used by Julius Caesar: Every letter is shifted a fix number of spaces to left/right of the alphabet and the shifting is the key for this alg. It's one of the oldest encryption methods. Example: A CAT can be shifted by 2 to give C ECV
- Easy to crack because of letter/word frequency: Some letters are used more
key: Number used by alg. to encrypt/decrypt a msg (Example: AES 128-bit)
plain text: Text you wish to encrypt
cipher text: Result of text after you add the alg. and key
Atbash Cipher:
Hebrew code which substitutes the first letter of the alphabet for the last and the 2nd letter for the second to last etc.. Basically reverses the alphabet.
A = Z, B = Y, C = X
Affine Cipher:
Any single-subtitution alphabet cipher (mono-alphabet substitution) in which each letter in the alphabet is mapped to some numeric value, permutated with some simple math function, then converted back to a letter
formula: ax +b (mod M)
m = Size of alphabet
x = Plain text numeric equivalent
b = The shift
a = Some multiple (Caesar is Z)
Caesar cipher: 1x + 3 (mod 26)
1[multiple]x[plain txt letter numeric equiv] +3[shift] (mod 26 [size of alphabet])
ROT13 Cipher: ROT = Rotation, 13=Number of rotation
Skytale:
Cylinder tool used by Greeks often attributed to Spartans. Cylinder used to encrypt msgs produced different cipher text first mentioned in the 7th century BCE by poet Archilochus. The writer wraps parchment around a rod, while the recipient uses the rod of a same diameter to decipher.

Single-Subtitution Weaknesses:
- Literacy rates have risen
- Lang has letter/word frequency
- Vulnerable to cryptanalysis
Multi-Alphabet Substitution:
Rotating through various keys in a cipher. Example: +1 -1 +2
* Key adds 1 to 1st letter, subtracts 1 from 2nd letter, adds 2 to 3rd letter
* Examples: Cipher disk, Vigenere, Enigma machines
Cipher Disk:
1466: Invented by Leon Alberti and was poly-alphabetic (each turn of the disk would produce a new cipher)
Vigenere Cipher:
1553: Giovan Battista Bellaso: Most widely known poly-alphabetic cipher
Uses a series of different mono-alphabetic ciphers selected based on the letters of a keyword. Commonly misattributed to Blaise de Vigenere even though he didn't really invent it. Used in the 1800's and early 1900's
Breaking the Vigenere Cipher: 1863: Friedrich Kasiski
Kasiski was the 1st person to publish a successful attack on the cipher that didn't rely on knowledge of plain text
Playfair Cipher: 1854: Charles Wheatstone
This cipher was named after Lord Playfair who promoted its usage. It encrypts 2 letters instead of just 1 and uses a 5x5 table containing a keyword or phrase.
Example: cheeseburger = ch ee se Bu rg er
ADFGX Cipher: 1918 Colonel Fritz Nebel
This was the first cipher used by the German Army in WWII and was transposition based. It used a modified polybius square (6x6), a single columnar transportation and a 36 letter alphabet.
Homophonic Substitution:
One of the earliest attempts to make substitution ciphers more robust by masking letter frequencies. Plain text letters map to more than 1 cipher text symble and use nomenclator.
Nomenclator: Combined a codebook that had a table of homophonic substitutions
Null Ciphers: Message is hidden in unrelated text but the sender/receiver have pre-arranged to use some pattern
Book Ciphers:
They've been around as long as books have and both parties agree to use a particular book as the basis: Coordinates are sent for words, so 3, 3, 10 would be Page 3, line 3, 10th word.
Rail Fence Ciphers: Maybe the most widely known transposition cipher that takes the message and alters each letter on a different row
A t c a d w
t a k t a n
(attack at dawn)
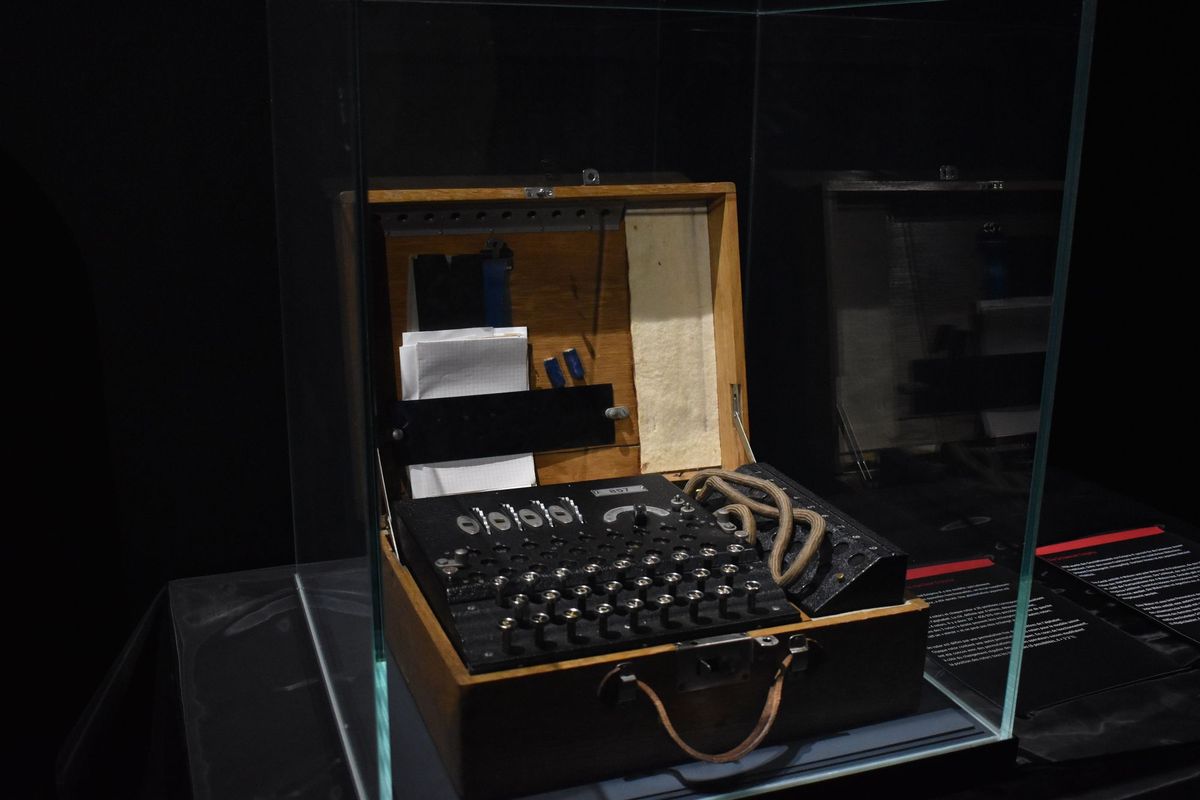
Enigma Machines: WWII:
Germans made use of an electro mechanical rotor based cipher system called an enigma machine. When the operator pressed a key, the encrypted text for that plain text was different every time. It was a multi-alphabet cipher with 26 possible alphabets.
Allied Cipher Machines:
- British Type X
- American SIGABA
- Contained more improvements/security
Cryptanalysis: Using other techniques to attempt to derive a key (other than brute forcing). To test hash algs for collisions and algs.
Kasiski's Method: Can be used to deduce the length of the keyword used in the poly-alphabetic substitution ciphers. Once the length of the keyword is found you can lineup cipher text in n columns where n is the length of the keyword
It's cracked with simple frequency analysis.
